Boost Efficiency with Desktop Monitoring
Discover how desktop monitoring software boosts employee productivity, reduces idle time, and helps your team work smarter every day.

Do you actually know how your team spends their workday? The detail here sits inside a wider conversation covered in our enterprise employee monitoring guide.
You see them logged in. You see tasks moving through the board. But between login and logout, you miss what happens in between. Time gets lost in distractions, idle periods, and apps that do not contribute to work. It is not always about effort. Sometimes the time is simply going to the wrong place, and without visibility into that, there is no way to catch it before it starts affecting results.
That is exactly where desktop monitoring helps. This blog covers what it is, how it creates real efficiency gains, and what to do with the data it gives you. By the end, you will clearly understand how your team spends their time and how to take action to improve it.
What Is Desktop Monitoring Software?
Desktop monitoring software is a tool that tracks and records how employees use their computers during work hours. It captures data on applications, websites, keystroke activity, screenshots, and overall activity to measure employee productivity, ensure policy compliance, and strengthen security on company‑owned or remote desktops.
You install it on each system, and it runs quietly in the background, sending activity data directly to a dashboard. From that dashboard, you view time-spent reports, spot idle behavior, and catch anomalies such as unauthorized software or suspicious file transfers.
How Does Desktop Monitoring Improve Employee Productivity?
Desktop monitoring improves employee productivity by making work activity visible at every level, from individual focus patterns to team-wide workflows. When you can see exactly how your team uses time, you stop guessing and start fixing the right things. Here are the specific areas where that visibility creates real efficiency gains.
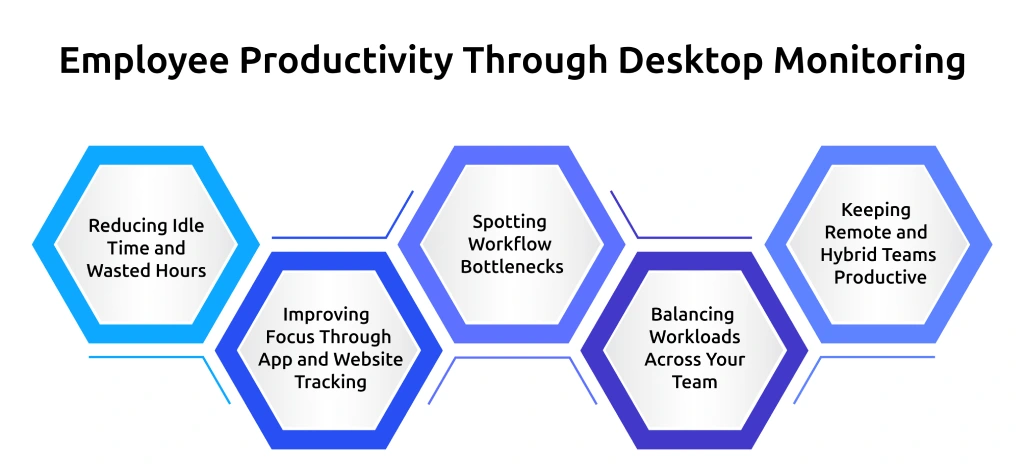
1. Reducing Idle Time and Wasted Hours
Desktop monitoring tracks how long each team member stays inactive during the workday. When idle time crosses a limit you set, you get an alert. You can check what the person was working on before the inactivity, spot what caused the delay, and fix it. Over time, identifying and removing these delays consistently helps you recover several productive hours each week.
2. Improving Focus Through App and Website Tracking
Employee desktop monitoring system tracks which applications and websites employees use during work hours, making it easier to identify distractions and guide better work habits. When teams clearly see how they spend their time across tools and sites, they can actively shift their attention toward tasks that drive meaningful progress.
3. Spotting Workflow Bottlenecks Before They Slow Your Team Down
Computer tracking software reveals delays in workflows by showing where tasks take longer than expected. Whether it is switching between tools or waiting on dependencies, these patterns become visible early. Teams can then address these issues before they impact deadlines or overall performance.
4. Balancing Workloads Across Your Team
You get a clear view of how work spreads across your team with desktop monitoring software. You can quickly spot who carries too much work and who has available capacity. With this insight, you redistribute tasks based on actual data, so no one carries an excessive workload while others have available capacity. This keeps your team balanced, consistent, and focused on delivering results.
5. Keeping Remote and Hybrid Teams Productive
Desktop monitoring provides consistent visibility across distributed teams. It maintains accountability without constant check-ins, helping you track progress and support work effectively. This creates a structured environment where your remote and hybrid team stays focused on the work that matters. If your team works remotely, choosing the right remote desktop monitoring software makes a direct difference in how well you can track and support them.
Guessing where productivity drops costs you more than you think.
Use Time Champ to track active time, identify idle patterns, and fix issues before they impact results.
How to Use Desktop Monitoring Data to Make Better Decisions?
Desktop monitoring gives you a constant stream of data about how your team works. But data on its own does not change anything. What changes things is knowing which numbers to pay attention to, what they are telling you, and what action to take based on what you see. That is where most teams either get value from monitoring or miss it entirely.
Start by looking at patterns rather than individual data points. A single idle period does not tell you much. But when the same pattern appears across multiple team members at the same stage of a workflow week after week, it signals that something in that process needs attention. When you read the data at that level, you stop reacting to surface-level numbers and start making decisions that fix the actual problem underneath. If your team works across more than one system, knowing how to track time on multiple desktops like Time Champ gives you a more complete picture of where hours actually go.
Does Desktop Monitoring Affect Employee Trust?
A survey by ExpressVPN found that 59% of workers feel that digital tracking damages trust at work, and 56% report feeling stressed and anxious due to excessive monitoring. Those numbers are real, and they point to a genuine concern that deserves a straight answer. Monitoring does not automatically reduce trust. The way you introduce monitoring and communicate it to your team determines whether it builds confidence or breaks it. Here is what actually makes the difference.
- Be Upfront About What You Track: Tell your team exactly what the software monitors, why you are using it, and how the data gets used. When the purpose is clear from the start, monitoring feels less like surveillance and more like a shared system everyone understands.
- Keep the Scope Focused on the Work Activity: Monitoring app usage, active time, and productivity patterns is very different from reading messages or tracking personal behavior. Staying within the boundaries of work-related activity is what separates a productivity tool from an invasion of privacy.
- Use the Data to Help, Not to Judge: When your team sees that monitoring data leads to clearing blocked tasks, fixing workflow issues, and balancing workloads more fairly, the perception shifts. It stops feeling like a tool used against them and starts feeling like something that works in their favor.
- Make the Results Visible to Your Team: Sharing insights like time spent on tasks, idle patterns, and app usage, along with the decisions made from them, builds credibility. When your team can see the outcomes, they understand the value and the intent behind the monitoring.
- Give Your Team a Voice in the Process: Involve your team early before you introduce monitoring. When they understand why it is being implemented and have space to ask questions, adoption becomes smoother and trust remains strong.
How Does Time Champ Work as a Desktop Monitoring Solution?
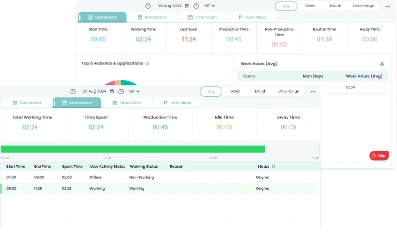
Time Champ is a desktop monitoring software that gives you complete visibility into how your team spends their workday. It tracks app usage, active and idle time, websites visited, productivity patterns, and screen activity across every work computer in your team, all feeding into one centralized dashboard you can check at any time.
What makes it useful beyond just collecting data is how it helps you turn that data into clear actions. You can set idle time thresholds, classify apps by productivity level, compare activity across your team, and get real-time alerts when something needs your attention. Whether you are reviewing your employees' daily activity or responding to an alert, you always have the information you need to make a clear call on what needs attention and what can wait.
Conclusion
Desktop monitoring brings clarity to how work actually happens every day across your team. It helps you catch productivity gaps early, keep workloads balanced, and make decisions based on what the data shows rather than what you assume. When monitoring fits naturally into your team’s workflow and you consistently act on the insights, efficiency becomes a result you sustain instead of a goal you keep chasing.
Still finding out about productivity issues after they affect results?
Use Time Champ to monitor desktop activity, catch issues early, and keep your team on track.
Table of Content
-
 What Is Desktop Monitoring Software?
What Is Desktop Monitoring Software?
-
 How Does Desktop Monitoring Improve Employee Productivity?
How Does Desktop Monitoring Improve Employee Productivity?
-
 How to Use Desktop Monitoring Data to Make Better Decisions?
How to Use Desktop Monitoring Data to Make Better Decisions?
-
 Does Desktop Monitoring Affect Employee Trust?
Does Desktop Monitoring Affect Employee Trust?
-
 How Does Time Champ Work as a Desktop Monitoring Solution?
How Does Time Champ Work as a Desktop Monitoring Solution?
-
 Conclusion
Conclusion
Related Blogs
Desktop monitoring software is a technological approach that organizations use to record and study the activities, as well as the output of persons who are working with computers provided by the organization.
Mounika Sai | Aug 24, 2023Explore the top 10 remote desktop monitoring software to enhance your team's productivity. Find the perfect tool with detailed features, pricing, and ratings.
Tarun Kumar Reddy | Aug 09, 2024Break the productivity barriers using PC monitoring software. Boost efficiency and address work challenges with effective monitoring solutions.
Mounika Sai | Aug 10, 2023Master PC monitoring software with our comprehensive guide. Discover benefits, best practices, and expert insights for enhancing security and productivity.
Thasleem Shaik | Dec 15, 2023Uncover security insights with keyloggers. Explore the technology behind every key for robust PC monitoring and ensure secure data management.
Mounika Sai | Jan 06, 2024Maximize productivity with comprehensive PC Activity Monitoring. Track, analyze, and optimize work habits for peak efficiency and performance.
Mounika Sai | Jan 09, 2024