Stealth Tracking: When It Works, When to Avoid It
Stealth tracking can improve visibility, but it also raises legal and trust concerns. Learn when it works and when transparent monitoring is the right choice.
Stealth tracking may seem like the easiest way to understand how work really happens inside your organization. Since employees do not know monitoring is active, you may expect more natural productivity data, fewer distractions, and better visibility into daily operations.
Hidden monitoring may give you more visibility, but it can also slowly weaken employee trust over time. Stealth tracking can support legitimate use cases like insider threat investigations or regulated environments. However, using it too broadly can create more problems than it solves.
This guide explains how stealth tracking works, when it makes sense, the risks you need to know, and why transparent monitoring often works better for modern teams.
What Is Stealth Tracking?
Stealth tracking is a type of employee monitoring that runs silently in the background without showing employees visible alerts, notifications, or tracking dashboards. It collects workplace activity data such as app usage, websites visited, active time, and productivity patterns while remaining hidden from the employee’s screen.
Unlike regular employee monitoring, stealth tracking operates without visibly notifying employees that monitoring is active. In transparent monitoring, employees can usually access dashboards, receive notifications, or view activity reports. While both approaches may collect similar workplace activity data, the main difference is visibility rather than the type of data captured.

Did you Know?
45% of monitored employees say workplace monitoring negatively affects their mental health, compared to 29% of employees who are not monitored.
Working Process of Stealth Tracking
Stealth tracking works by running employee monitoring software silently in the background while collecting workplace activity data for you to review. Unlike transparent monitoring tools, your employees usually do not see visible notifications, dashboards, or tracking alerts during use.
Most stealth tracking systems follow a simple process that includes installation, background activity collection, data reporting, and tamper protection.
1. Installation and Setup
Install the tracking software on company devices with stealth settings enabled. Depending on the tool you choose, the software may hide startup notifications, desktop icons, or taskbar visibility. Some systems also place files in protected system folders, making removal difficult without administrator access.
During setup, you can usually decide:
- What activities do you want to monitor
- Which teams or devices do you want to include
- Whether you need screenshots or activity logs
- How long do you want to store the data
Modern tools also let you limit monitoring to work-related activities only.
2. Background Activity Monitoring
Once active, the software quietly records activity throughout the workday without interrupting your employees’ workflow.
Depending on your settings, the system captures:
- Applications used
- Websites visited
- Active and idle time
- Login and logout activity
- File transfers
- Keystroke counts
- Screenshot intervals
Most enterprise tools avoid recording actual keystroke text because collecting sensitive personal information increases legal and privacy risks.
3. Data Transmission and Reporting
The system securely sends collected data to your administrator dashboard, where you can review productivity trends, attendance patterns, and unusual activity.
You can typically access:
- Productivity summaries
- Time usage reports
- Attendance insights
- Application usage data
- Potential security alerts
The reporting experience usually looks the same as transparent employee monitoring systems. The main difference is that the software operates invisibly on the employee’s device.
4. Tamper Protection
Many stealth tracking tools include features that help you prevent standard users from disabling or removing the software.
These protections may include:
- Restricted uninstall permissions
- Hidden background processes
- File protection mechanisms
- Alerts when tampering is detected
This is one of the main differences between true stealth tracking software and regular monitoring tools running in hidden mode.
Want better visibility without damaging employee trust?
See how Time Champ helps you monitor productivity more transparently.
4 Legitimate Use Cases for Stealth Tracking
Stealth tracking is not something you should use across your entire organization by default. In most workplaces, transparent monitoring creates better trust, stronger communication, and healthier employee relationships.
However, stealth tracking justifies itself in a few specific situations when you have a clear business reason and proper legal oversight.
1. Active Insider Threat Investigations
If you already have evidence of data theft, policy violations, or suspicious behavior, open monitoring can immediately alert the person involved.
In these situations, stealth tracking may help you preserve evidence without disrupting the investigation. For example, if someone transfers confidential files outside your organization, hidden monitoring can help you confirm what is happening before taking action.
2. Regulated Industry Compliance
If you operate in industries like finance, healthcare, or government contracting, you may need continuous activity logging to meet compliance requirements. Regulations tied to HIPAA, SOX, FINRA, or FedRAMP often require detailed records of system access and employee activity.
In many of these environments, monitoring is already disclosed in onboarding documents or employment contracts. The software may run invisibly, but your employees are still informed that monitoring exists.
3. High-Sensitivity Roles with Pre-Disclosure
Some teams handle highly confidential information every day. This may include:
- Research and development teams
- Intellectual property divisions
- Defense contractors
- Security operations teams
In these cases, you may need stronger monitoring controls to protect sensitive data.
The safest approach is usually a “disclosed stealth” model where you clearly explain monitoring policies during onboarding while keeping the software non-intrusive during daily work.
4. Forensic Investigations After Security Incidents
After a confirmed breach or policy violation, you may need activity records to understand what happened.
Stealth tracking can help you review:
- Access history
- File movement
- Login activity
- System behavior before the incident
This information may support internal investigations, legal reviews, or compliance reporting. In these situations, the goal is evidence preservation rather than day-to-day productivity monitoring.
| Stealth tracking is the right call when: | Stealth tracking is the WRONG call when: |
|---|---|
| You're investigating a specific, documented incident | You just want general productivity insights |
| Compliance regulations require continuous logging | Your goal is to catch slackers |
| Roles handle classified or IP-sensitive work, with disclosure | You haven't disclosed monitoring in employment contracts |
| You have legal counsel signing off on the deployment | Your team is in CT, DE, NY, CO, CA, or under GDPR/EU AI Act |
| It's time-bounded and tied to a specific investigation | You're rolling it out across the whole team by default |
| You can justify the business need in writing | You're hoping employees never find out |
Is Stealth Tracking Legal?
Yes, stealth tracking can be legal in some situations, but the rules depend on where your employees work, what data you collect, and whether you disclose the monitoring properly. A setup that works legally in one region may create compliance issues somewhere else, especially if your team works remotely across multiple states or countries.
US Federal Laws
In the United States, federal law generally allows you to monitor company-owned devices when you have a legitimate business reason, such as security, compliance, or operational protection. This gives you some flexibility to monitor workplace systems and employee activity during work hours.
However, the rules become stricter when your monitoring involves personal devices, private accounts, sensitive personal information, or hidden surveillance without disclosure. Federal law provides a baseline, but it does not give you unlimited monitoring rights in every situation.
State Notification Requirements
Several US states now require you to notify employees before monitoring takes place. These notification laws are becoming more common as workplace privacy concerns continue to grow.
For example, Connecticut and Delaware require written notice before monitoring begins. New York requires both written notice and workplace posting requirements. Colorado has introduced notice requirements for AI-driven monitoring systems, while California requires disclosure when you collect personal information.
GDPR and International Privacy Laws
If your employees work in Europe or other regions with strict privacy regulations, stealth tracking becomes much harder for you to justify legally.
Under GDPR, you must clearly explain what data you collect, why you collect it, how long you store it, and who can access it. Since stealth tracking operates invisibly, it often conflicts with GDPR transparency requirements for routine employee monitoring.
Because monitoring laws continue to evolve, you should carefully balance legal compliance, transparency, and employee trust before using stealth tracking in your workplace.

Did you Know?
96% of workers are comfortable with workplace monitoring when they clearly understand its benefits and purpose.
5 Risks of Stealth Tracking You Need to Know
Stealth tracking may give you deeper visibility into employee activity, but it can also create risks that are difficult to control once monitoring becomes known. In many cases, the biggest problems do not come from the software itself. They come from how your employees react when they discover hidden monitoring inside the workplace.
1. You Can Lose Employee Trust Quickly
Once your employees realize they are being monitored secretly, rebuilding trust becomes extremely difficult. Even your most dependable team members may begin questioning your leadership decisions, workplace transparency, and company culture. Instead of feeling supported, employees may feel watched or controlled, which can create fear, frustration, and emotional distance within the workplace.
2. You May Face Legal Problems Across Different Locations
If your employees work across multiple states or countries, managing and monitoring compliance becomes much more complicated. This is especially challenging when you manage remote teams, hybrid employees, or international staff. As employee monitoring laws continue to evolve, companies must carefully review regional requirements before using stealth tracking to avoid legal exposure and compliance issues.
3. Your Brand Reputation Can Be Damaged Publicly
Employees frequently share workplace experiences online, especially when they feel uncomfortable with company policies or monitoring practices. If hidden tracking becomes public, discussions about your company may quickly appear on platforms like Glassdoor, Reddit, LinkedIn, or social media. This can lead to negative employer reviews, hiring challenges, public criticism, and loss of employee confidence.
4. You May End Up with Misleading Productivity Data
Many companies assume stealth tracking automatically creates more accurate productivity insights, but that is not always true. Once employees discover hidden monitoring, they often begin changing their behavior to appear active rather than work naturally. You may start noticing fake mouse movement, unnecessary app switching, and inflated online presence.
5. Your Monitoring Software Can Become a Security Risk
Stealth tracking software is designed to resist removal, but this can sometimes create additional security concerns for your IT team. If the software is not updated properly, hidden background agents may become vulnerable to attacks or system conflicts. An effective monitoring tool can introduce security gaps, outdated processes, and unauthorized access risks into your environment.
Before you use stealth tracking, you should think carefully about whether the extra visibility is worth the legal issues, workplace problems, and trust concerns it may create. In many workplaces, transparent monitoring helps you build better trust, avoid unnecessary problems, and gain stronger support from your employees.
CTA
Ready to replace hidden tracking with transparent productivity insights?Discover how Time Champ balances visibility, accountability, and employee privacy.
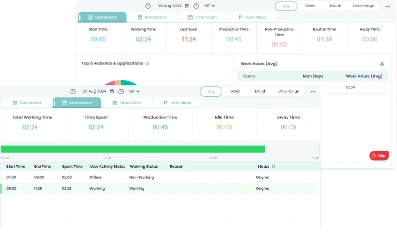
Time Champ: A More Transparent Approach to Employee Monitoring
In many workplaces, transparent monitoring creates better long-term results than hidden tracking. When your employees clearly understand what is being monitored and why, you can build stronger trust, healthier communication, and better accountability across your teams.
That is why Time Champ focuses on transparent employee monitoring instead of hidden surveillance by default. With Time Champ, you and your employees can view the same productivity insights, which helps monitoring feel more collaborative and less intrusive. At the same time, you still get the visibility you need to manage daily operations effectively. Time Champ helps you monitor:
- Productivity trends
- Application and website usage
- Active and idle time
- Attendance patterns
- Workload distribution
- Team performance insights
To support secure and flexible monitoring, Time Champ also gives you role-based access controls, configurable tracking settings, and detailed activity reports. This helps you maintain better visibility across your teams while keeping monitoring transparent, structured, and employee-friendly.
Instead of depending on hidden surveillance, you can create a more balanced monitoring approach that improves accountability, operational clarity, and workplace trust.
Conclusion
Stealth tracking can support a few legitimate business needs, especially during security investigations, compliance reviews, or high-sensitivity operations. However, using it as a default monitoring strategy can create legal concerns, weaken employee trust, and damage workplace culture over time. Before you implement stealth tracking, you should carefully evaluate whether the extra visibility truly supports your business goals or simply creates more risk and uncertainty for your team.
Table of Content
 What Is Stealth Tracking?
What Is Stealth Tracking? Working Process of Stealth Tracking
Working Process of Stealth Tracking 4 Legitimate Use Cases for Stealth Tracking
4 Legitimate Use Cases for Stealth Tracking Is Stealth Tracking Legal?
Is Stealth Tracking Legal? 5 Risks of Stealth Tracking You Need to Know
5 Risks of Stealth Tracking You Need to Know Time Champ: A More Transparent Approach to Employee Monitoring
Time Champ: A More Transparent Approach to Employee Monitoring Conclusion
Conclusion
Related Blogs
Stealth and transparent monitoring work very differently for teams. See the key differences, legal implications, and which approach fits your organization.
Jahnavi Pulluri | Apr 21, 2026Stealth monitoring can expose your business to legal risks. Learn the key challenges, compliance issues, and how to monitor employees effectively.
Guna Lakshmi | Apr 28, 2026Learn how to choose the right remote employee monitoring software with the right features, scalability, and usability to manage remote teams effectively.
Guna Lakshmi | Apr 14, 2026Explore how to implement employee monitoring software effectively with clear steps, legal tips, best practices, ROI metrics, and key pitfalls to avoid.
Anjali | Apr 15, 2026Learn how to legally implement employee monitoring software. Covers legal requirements, policy steps, best practices, and what to tell your employees.
Thasleem Shaik | Apr 16, 2026The AI employee monitoring software goes beyond basic tracking. It predicts risks, reveals patterns, and gives you real clarity to lead your team better.
Shabana Shaik | Apr 17, 2026