Legal Implications of Monitoring Personal Devices: A Compliance Guide
What is legal and what is risky when monitoring employee personal devices? A 2026 compliance guide covering consent, BYOD law, state notices, and global rules.

If you have ever sat in a meeting and someone asks, "Can we just install monitoring software on their phones?" and watched the room go completely silent, you already know what the issue is. Monitoring personal devices is one of those workplace decisions that looks simple on the top and gets very complicated very fast once you read the laws concerning it.
My honest answer is that you can monitor personal devices in most jurisdictions, but only if you adopt the right approach, with the right paperwork, in the right scope, and that too with the right safety net for the data you collect.
If you get even one of those wrong, then the productivity gain you were chasing turns into a lawsuit, a regulator letter, or a quiet PR mess.
This guide is the version I wish I had when I first started writing about workplace monitoring (now you have it). I'll be covering what counts as personal device monitoring, what the law actually says in the US, EU, UK, Canada, and APAC, where the real legal risks sit, the seven-step compliance framework that keeps you out of trouble, what your BYOD policy must include, and the cases where the smartest call is to not monitor at all.
I know this is very legalese stuff, but I'll try to put it in as simple English as possible.
What Does "Monitoring Personal Devices" Actually Mean?
Personal device monitoring is the practice of collecting work-related activity data from a device that the employee owns and brings to the job. It can include time tracking, app and website usage, screenshots, location, network access, message metadata, and remote-wipe capability. The scope varies enormously, and the law treats different scopes very differently, which is why the first job is to define what you actually mean by "monitoring."
BYOD vs COPE vs CYOD: Why the Distinction Matters
These three labels look interchangeable, but they are not, and the legal posture changes with each.
BYOD (Bring Your Own Device)means the employee owns the hardware. The employer accesses work data on it through policy, consent, and usually an MDM (mobile device management) profile. Employee privacy expectations are highest here.
COPE (Corporate-Owned, Personally-Enabled)means the employer owns the device, but the employee can use it for some personal tasks. Employer latitude is broader because the hardware is theirs, but private communications still get protection.
CYOD (Choose Your Own Device)means the employer buys from a pre-approved list, and the employee picks. Ownership stays with the company, so legally, CYOD usually behaves like COPE.
If you skip this distinction and simply write a single policy for "personal devices," you will end up over-claiming on BYOD and under-claiming on COPE, and your monitoring program will fall apart the first time someone challenges it. If you want to know more on BOYD and its benefits, you can read our blog.
What Kinds of Monitoring are we Even Talking About?
The word monitoring is not restricted to just overseeing, it covers a wide range. The legal risk scales roughly with how invasive the data collection is. From lightest to heaviest:
• Time and attendance tracking
• Work app and website usage during work hours
• Project and task time tracking
• Network activity on the corporate VPN
• GPS location during work hours
• Screenshots of work apps
• Keystroke logging
• Live screen recording
• Camera or microphone access
Anything in the lower half of this list, on a personal device, is where most legal troublemakers make a living. The safer monitoring stack on a BYOD device focuses on time, attendance, work-app usage, and location during work hours, with the heavier signals reserved for company-owned devices.
Is it Legal to Monitor Employee's Personal Devices?
The short answer is yes, in most jurisdictions, when three conditions are met.
- First, you have informed, voluntary, ideally written consent.
- Second, the monitoring serves a clear and reasonable business purpose, documented in policy.
- Third, the scope is narrow and proportionate, with private communications, off-hours activity, and personal apps excluded.
Skip any one of those three, and the monitoring becomes legally unsafe, even if a piece of paper somewhere says it is allowed. Courts and regulators look at the actual practice, not the policy text alone.
A second short answer that practitioners often miss: even when monitoring is lawful, the data you collect inherits a separate set of obligations under privacy law. Storage, access, retention, and cross-border transfer rules all apply once the data is in your hands.
Which Laws Govern Personal Device Monitoring in 2026?
The legal map for personal device monitoring is not one law, it is a stack of laws that overlap and sometimes conflict. Here is the practitioner’s view.
United States: ECPA, CFAA, and The Four-Corners-of-the-State Rule
The Electronic Communications Privacy Act (ECPA) is the federal baseline. It generally prohibits intentional interception of electronic communications, with two big exceptions.
The First one: Monitoring is allowed if at least one party consents to it.
Second One: Monitoring is allowed in the ordinary course of business when the employer has a legitimate operational reason.
Penalties for ECPA violations can run up to $250,000 in fines and up to five years in prison, plus civil damages.
The Computer Fraud and Abuse Act (CFAA) sits next to ECPA and reaches "unauthorized access" to computers. CFAA matters most when an employer reaches further into a personal device than the employee actually authorized.
State law sits on top of both. Some states are more protective than the federal floor, and the federal floor is the minimum, never the ceiling.
State Notice Laws to Know
Several US states require employers to give specific written notice before any electronic monitoring begins. These are the main ones:
| State | What's Required |
|---|---|
| Connecticut | Prior written notice of all electronic monitoring, posted conspicuously |
| Delaware | Daily notice or one-time written notice acknowledged by the employee |
| New York | Written notice at hire and annual renewal, plus posted notice in the workplace |
| Colorado | Written notice is required under the Colorado Privacy Act when sensitive data is processed |
| Illinois | BIPA-driven notice rules for biometric data, plus general consent best practice |
Even in states without a specific statute, written notice is the practical baseline because it neutralizes the "we did not know" defense an employee might raise later.
European Union: GDPR
GDPR governs the monitoring of any EU resident’s personal data, regardless of where the employer sits. Six things to keep in mind.
- First, you need a lawful basis. Consent is one, but for employer-employee relationships, regulators often prefer "legitimate interests" backed by a documented assessment, because employee consent is rarely seen as fully voluntary.
- Second, you must be transparent.
- Third, you must be proportionate (you collect only what you need).
- Fourth, you must give employees data subject rights.
- Fifth, you must run a Data Protection Impact Assessment (DPIA) for any monitoring that is "systematic."
- And sixth, you must purge data on a documented schedule.
GDPR fines reach €20 million or 4% of global annual turnover, whichever is higher. Most monitoring fines published in the last few years sit between €50,000 and €5 million, but the headline cases (large retail and logistics employers) have run higher.
United Kingdom: UK GDPR and Data Protection Act 2018
The UK left the EU but kept the GDPR framework as UK GDPR, paired with the Data Protection Act 2018. The Information Commissioner’s Office (ICO) published updated guidance on workplace monitoring that aligns with GDPR principles and adds practical advice on covert monitoring (only allowed in narrow misconduct investigations) and data minimization.
Canada: PIPEDA and Provincial Laws
The Personal Information Protection and Electronic Documents Act (PIPEDA) covers most of Canada. British Columbia, Alberta, and Quebec have their own provincial privacy laws that often add additional consent and transparency requirements. Quebec’s Law 25 is the strictest in the country and is worth a separate review for any employer with Quebec staff.
Asia-Pacific
The legal map varies more in APAC than anywhere else.
• Indiahas the Digital Personal Data Protection Act (2023), which sets the consent and notice rules, and these are pretty much the same as GDPR for personal data processing.
• Australiahas the Privacy Act, with the Australian Privacy Principles (APPs), which require you to notify employees at the time of data collection and for a lawful purpose. Plus, certain areas of Australia require electronic monitoring policies in writing.
• Singapore'sPersonal Data Protection Act (PDPA) requires you to have employee consent and purpose limitation.
• Japan, South Korea, and the Philippines each have their own privacy laws with varying consent and transparency requirements.
If you want to understand these laws better, you can head over to our blogs on employee monitoring legal compliance guide and understanding employee monitoring laws.
Want to ensure employee trust through monitoring?
Try Time Champ's vast yet privacy driven features and ensure your team's trust.
What are the Biggest Legal Risks of Monitoring Personal Devices?
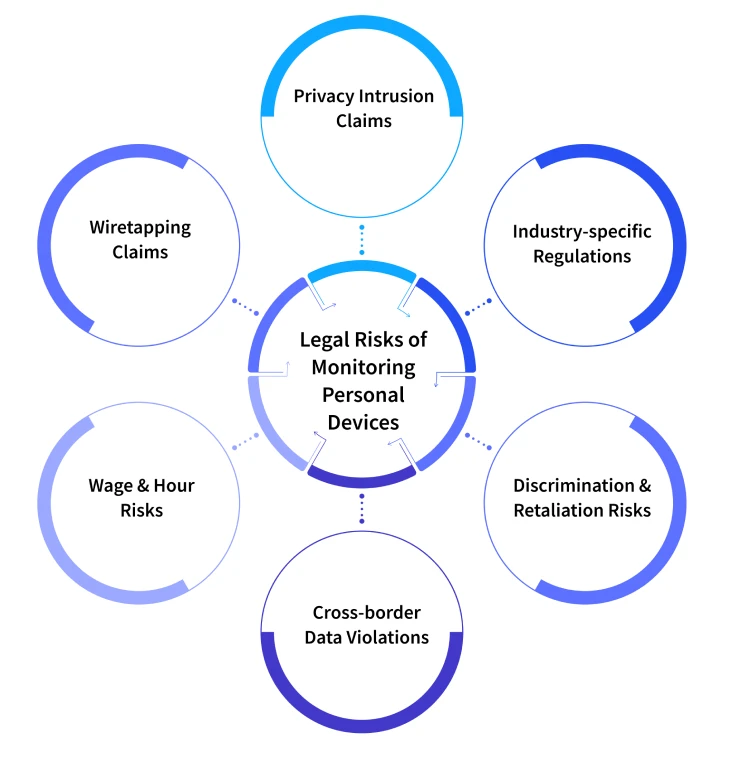
This is where most companies get surprised, and when you don't know the consequences, surprises are unavoidable. FYI, these risks are not always the ones HR is watching for.
1. Privacy and Intrusion-on-Seclusion Claims: When monitoring reaches into a part of the device that an employee reasonably considers private, such as taking photos, personal email, banking apps, for example, then the employee can sue for invasion of privacy in most US states. Damages have no upper limit, and juries usually sympathize with the employee.
2. Wiretapping and Unauthorized Interception Claims: ECPA and state wiretap laws apply to live capture of communications, reading a saved message is usually fine, but intercepting a live call or chat without the employee's consent is absolutely not.
3. Wage and Hour Exposure: This one commonly surprises people. If your monitoring software shows employees working off the clock on a personal device, you may have created a wage and hour claim. Federal Fair Labor Standards Act (FLSA) and state wage laws require non-exempt employees to be paid for all hours worked, and that includes "voluntary" off-hours work the employer knew about or should have known about.
4. Cross-border Data Transfer Violations: GDPR’s rules on transferring personal data outside the EU apply the moment a US-based monitoring server pulls activity data from a personal device used by an EU employee. Standard contractual clauses, transfer impact assessments, and the EU-US Data Privacy Framework now sit between you and a fine.
5. Discrimination and Retaliation Exposure: Monitoring data that flags only some employees, or that disproportionately affects a protected group, can be Exhibit A in a discrimination claim. The same goes for using monitoring data to retaliate against an employee who raised a concern.
6. Industry-specific Overlay: Healthcare under HIPAA, financial services under GLBA, education under FERPA, public sector under union or civil-service rules. These are not a replacement for baseline privacy law, they sit on top, and a compliant program addresses both layers.
How to Build a Legally Compliant Personal Device Monitoring Program?
Here is the seven-step framework I have walked through with HR and Legal teams more times than I can count. It works because it puts the paperwork and the engineering on the same calendar, instead of treating them as separate tracks.
- Decide Your Device Model First: BYOD, COPE, or CYOD. Write it down before anything else. The legal posture flows from this single decision.
- Map Every Jurisdiction Your Employees Sit in: Including remote workers and contractors. The strictest applicable law sets your baseline.
- Define the Narrowest Possible Scope: What data do you actually need? Time and attendance? App usage during work hours? Location for field work? Write the list and stop there.
- Write the Policy, in Plain English: What is collected, when, by whom, where it is stored, how long, who can access it, and what decisions it informs.
- Get Written, Voluntary Consent: Onboarding signature is the baseline. Annual reaffirmation is better. For EU employees, lean on legitimate interests with a DPIA, not employee consent.
- Configure Tooling to Match the Policy: This is where most programs fail. The tool can collect more than the policy permits, and a misconfiguration becomes a violation. Audit the configuration before launch.
- Set up Retention, Access Controls, and a Complaint Channel: Auto-purge raw data on a clear schedule. Role-based access, so the data only reaches the people who actually need it. A confidential way for employees to ask questions or raise concerns without fear of retaliation.
If you do these seven steps in order, you have a defensible program. Skip any one of them, and a single complaint can unravel the rest.
Want Ethical Monitoring for Your Business?
Time Champ is an ISO Certified platform that complies with GDPR, HIPAA, and SOC for utmost employee privacy.
What to Include in a BYOD Policy to Make Monitoring Legal?
A defensible BYOD policy reads less like a contract and more like a clearly written user agreement. Here is what every section needs.
• Scope and Ownership: Which devices, which employees, which apps. Who owns the hardware, who owns the data.
• What is Monitored, in Plain Words: Not just "activity" but the actual list, in employee-readable language.
• What is Not Monitored: Personal apps, personal photos, off-hours activity, private communications. Naming what is excluded matters as much as naming what is included.
• Consent and Acknowledgement: A signature line, with a date, and a copy provided to the employee.
• Use of Data: What decisions does it inform? Performance reviews? Workload rebalancing? Security investigations? Be specific about it.
• Retention: How long the data is held, and what triggers data deletion.
• Access: Who can see the data, in what role, and under what circumstances.
• Employee Rights: Right to see their own data, right to correct, right to delete in jurisdictions that allow it.
• Off-boarding: What happens when the employee leaves the company. Selective wipe of work data, full audit log of what was wiped.
• Complaint Channel: Where to raise concerns, with explicit anti-retaliation language.
• Jurisdiction-specific Addenda: Required notice language for states that mandate it, GDPR-specific clauses for EU employees.
If your existing policy is missing more than two of the above, it is not just out of date, it is exposed.
When is Monitoring Personal Devices NOT Worth the Legal Risk?
If you know when to monitor personal devices, things get easy, but when you know where not to use monitoring on personal devices, things get better because, sometimes, the right answer is not to monitor at all. Here are the four scenarios where I would consciously walk away from a personal-device monitoring plan.
Scenario 1:
The team is small enough that one-on-ones and outcome tracking already give you visibility. A 12-person team rarely needs personal device monitoring. The cost of the legal review is higher than the productivity benefit.
Scenario 2:
The role is fully exempt and outcome-based. If the employee is judged on deliverables, not hours, monitoring personal device activity adds risk without adding signal.
Scenario 3:
You have a heavy GDPR or jurisdictional exposure. The cross-border compliance cost on a small EU footprint can swamp the benefit. Issue company devices to those employees instead.
Scenario 4:
The actual concern is security, not productivity. If the real worry is data leak from personal devices, the right tool is enterprise mobility management with data containerization, not productivity monitoring.
The right thing you need to ask yourself before committing to any kind of monitoring is discipline is, "What problem am I actually trying to solve?" before reaching for monitoring. Often, the answer points somewhere else than you think it is.
How Does Time Champ Approach Personal Device Monitoring Compliance?
Time Champ is employee monitoring software with workforce intelligence as a built-in feature, designed completely for visibility and compliance. On personal devices, the configuration choices that matter are: configurable screenshot frequency (or none at all on BYOD), category-level activity classification so personal apps stay invisible, tracking limited to defined work hours, and clear separation between team-level and individual-level reporting. Time Champ complies with GDPR, ISO 27001, HIPAA, and SOC 2, and it also supports the data subject rights GDPR requires.
If you want to know more about mobile workforces specifically, you can view our mobile tracking product page.
Most employee monitoring software stops at activity logs. Time Champ adds a workforce intelligence layer that surfaces team and org-level patterns, which is what gives the program a real return without forcing more invasive individual surveillance.
Key Points to Remember:
• Monitoring personal devices is legal in most jurisdictions when you have informed consent, a clear business purpose, and a narrow scope. Skip any one of those, and the program is exposed.
• The applicable law is a stack: federal ECPA in the US, state notice laws (CT, DE, NY, CO, IL), GDPR and UK GDPR in Europe, PIPEDA in Canada, and a varied APAC map.
• The biggest legal risks are not the obvious ones. Wage and hour exposure, cross-border data transfer violations, and discrimination claims often outrun the privacy claim.
• A compliant program follows seven steps: pick the device model, map jurisdictions, define a narrow scope, write a plain-English policy, get written consent, configure tooling to match, and set up retention plus access controls.
• Sometimes the right answer is to skip personal device monitoring entirely and issue company devices, especially for small teams, exempt roles, GDPR-heavy footprints, and security-driven use cases.
Table of Content
 What Does "Monitoring Personal Devices" Actually Mean?
What Does "Monitoring Personal Devices" Actually Mean? Is it Legal to Monitor Employee's Personal Devices?
Is it Legal to Monitor Employee's Personal Devices? Which Laws Govern Personal Device Monitoring in 2026?
Which Laws Govern Personal Device Monitoring in 2026? What are the Biggest Legal Risks of Monitoring Personal Devices?
What are the Biggest Legal Risks of Monitoring Personal Devices? How to Build a Legally Compliant Personal Device Monitoring Program?
How to Build a Legally Compliant Personal Device Monitoring Program? What to Include in a BYOD Policy to Make Monitoring Legal?
What to Include in a BYOD Policy to Make Monitoring Legal? When is Monitoring Personal Devices NOT Worth the Legal Risk?
When is Monitoring Personal Devices NOT Worth the Legal Risk? How Does Time Champ Approach Personal Device Monitoring Compliance?
How Does Time Champ Approach Personal Device Monitoring Compliance? Key Points to Remember:
Key Points to Remember:
Related Blogs
Learn about employee privacy rights, how to protect personal information, and balance company needs with privacy laws.
Jahnavi Pulluri | Sep 18, 2024Find the best GPS location tracking apps for employees to track routes, manage time across sites, and keep work organized with real-time insights.
Thasleem Shaik | Apr 13, 2026Employee surveillance vs employee monitoring: see the 8 key differences, how surveillance damages morale, and when transparent monitoring builds trust instead.
Jahnavi Pulluri | Apr 22, 2026Learn how remote employee tracking and DLP work together to prevent data leaks, secure remote teams, and support privacy, compliance, and safer workflows.
Anjali | May 09, 2026Protect your business from BYOD security risks like data breaches and phishing. Learn practical ways to secure employee devices and reduce security threats.
Guna Lakshmi | May 07, 2026Ensure remote work compliance with our guide on key areas, common challenges, and best practices for your team.
Shabana Shaik | Jan 10, 2025