What is Data Exfiltration? How to Detect & Prevent It
Learn what data exfiltration is and how to prevent it from attackers. Protect your business from data theft with effective security strategies and best practices.
If someone risks stealing or leaking your company’s sensitive data, such as financial records and client information, it’s hard to notice that type of fraud every time. Data exfiltration is a growing threat that exposes your business to breaches, legal troubles, and reputation damage. It is important to understand how data exfiltrates and how to prevent it effectively.
In this blog, we will explain what data exfiltration i, how it happens, and how to detect it. We will also provide actionable steps to prevent your organization from data exfiltration threats. Let’s dive in!
What is Data Exfiltration?
Data exfiltration is the unauthorized transfer of sensitive information from a personal or a company’s network to an external destination through various cyberattack methods. Exfiltrating data can be done in many ways. For example, it may happen through hacking, malware, or insider threats. Attackers can grab your company’s important information if they get into your systems. Exfiltration happens all the time without proper detection. You need to know how to detect and protect your organization from this type of threat.
How Does Data Exfiltration Occur?
Data exfiltration can happen in two main ways: by external attackers or insiders in your organization. Most external attackers gain unauthorized access to your network through phishing, malware, or in the worst case by exploiting weaknesses in your security protection. Once they log in to your system, they can access system data and transfer your company’s important information and files to an external server or location. Often these types of attacks occur through simple human error or the use of an insecure network, such as phishing attacks or when employees click a link in a phishing attack.
Your organization is also at risk from insider threats. Employees, contractors, or anyone who has authorized access to your company data have a chance to leak the company’s information intentionally or unintentionally. They may copy office files to their personal devices, send them by email, or upload them to unprotected cloud storage. But even without malicious intent, exfiltration can occur within your organization. You need to regularly monitor your systems to prevent unauthorized data transfers from internal and external attackers.
Prevent data exfiltration and keep your sensitive information safe!
Start using Time Champ to detect and stop threats before they happen!
Types of Data Exfiltration
Knowing the types of data exfiltration can let you know how to protect your organization in a better way. Let’s take a look at some of the most common ways attackers use to steal your company’s sensitive information.

1. Network-Based Exfiltration
In a network-based exfiltration, data is transferred from your internal network to an external destination. Hackers use malware, viruses, or any other software to gain access to your network. Then, they send your sensitive data to their servers. And, attackers commonly use encrypted channels to hide their activities, it can become even more difficult to detect. Often this type of exfiltration goes unnoticed due to its ability to blend in with regular network traffic and is hard to detect without the right monitoring tools.
2. Removable Media Exfiltration
Removable media exfiltration involves transferring data through portable devices like USB drives, external hard drives, or SD cards. If your employees or attackers have physical access to your systems, they can copy sensitive files to those devices and carry them outside the organization. Particularly, this type of exfiltration is riskier, if your organization doesn’t have tight security controls on removable media use. In addition, these devices are easily lost or stolen, and you might end up exposing your own data to someone else.
3. Cloud Storage Exfiltration
If you are using cloud storage highly in your organization, then exfiltration through these cloud platforms has become more common. There is a chance that your employees can also upload sensitive data to unsecured cloud storage services or personal accounts and not encrypt it properly. Once the data is uploaded, it will be accessible and can be stolen by attackers. You can reduce this risk by maintaining strong security measures and access controls. Also, your employees may accidentally upload sensitive data to a cloud platform that is not authorized and the possibility of a breach to your organization increases. In addition, implementing cloud cost optimization strategies helps ensure that storage usage remains efficient while maintaining compliance with your organization’s security policies.
4. Application-Based Exfiltration
Exfiltration based on application is when attackers take advantage of weaknesses in applications to take out data. If your employees install malicious applications in company devices or systems, then it’s easy for attackers to exfiltrate the data. If the app is once compromised then it can send the sensitive information to the external server without the user’s knowledge. You can prevent this type of exfiltration by regularly patching and updating your software.
5. Social Engineering Exfiltration
Social engineering exfiltration is the action of manipulating people to extract sensitive information. Mostly, this type of attacker uses phishing, impersonation, and pretexting tactics to trick your employees into sharing passwords or downloading malicious attachments. This type of exfiltration is especially dangerous to your organization. Because, this threat attacks human weaknesses, not technical vulnerabilities. To prevent your organization from those types of social engineering attacks, you can educate your team and help them recognize before attackers get into systems.
Stop Data Exfiltration Across All Channels!
Track threats, cloud breaches, and file transfers with Time Champ to protect your data.
The Cost of Data Exfiltration
Data exfiltration can be very costly for businesses, especially when sensitive information is stolen. When a data breach happens, you often have to pay for more than just fixing the problem. You also face other expenses that can add up quickly. The first thing you think about is the direct costs. You may need to pay for investigations, hire experts to make security stronger, and take better precautions. There may also be fines if customer or employee data is involved. Over time, these costs can really add up and hurt your company’s cash flow and profits.
Customers can lose trust in your company if you suffer a data breach. If they don’t feel that their personal information is safe, they may choose another company instead. Then, your sales may decrease and your company’s reputation also be damaged. It can take years, and a lot of time, work, and money to earn back your clients’ trust. There is nothing like data theft which can result in legal problems, more especially in a situation when your company does not adhere to data protection laws. If you can invest in your cybersecurity and train your team, you can save your company from the very high costs of data theft.
How to Detect Data Exfiltration?
It is important to find data theft early to minimize the damage. The first thing you need to do in data exfiltration detection is that you need to watch for unusual data transfers. If you find any large or unusual transfers to unknown places or devices often in your organization, it could be a breach. You need to set up automatic alerts to spot those big file transfers.
Also, you have to keep track of who is viewing or downloading the company’s sensitive data. It may be a warning sign if some of your employees are accessing information that is not part of their usual work. You can limit data access to only authorized users to prevent these problems easier.
Endpoint detection tools provide extra security by watching devices on your network for anything unusual. These tools can spot things like sudden changes in data usage, attempts to access locked information, or strange actions that aren’t typical for users. They also help set a normal pattern of activity, so it’s easier to notice weird things, like logins from unusual places or at odd times.
If your company uses cloud storage, cloud activity audits are important. Security tools exist in the cloud services that can track who is accessing, sharing, or downloading files. Also, you should watch out for email activity since emails are usually used to steal data through scams like phishing or harmful attachments. Data Loss Protection (DLP) tools can also detect when someone attempts to move important files without permission.
Data Exfiltration Prevention
You must take action before attackers steal your data. First, establish strong rules about who can view and who has access to handle the company’s confidential data. Allow permissions based on people’s job roles and recheck who further has access to crucial information. It’s also a good idea to add multi-factor authentication (MFA) which makes it harder for hackers to get into your systems even if they have someone of your employee’s password. And it’s also important to train your employees because mistakes can cause data breaches.
Basic cybersecurity and common threats like phishing are both methods that you can teach your team to help stop accidental leaks of sensitive information. Preventing data theft is important and that’s why network monitoring is important. You can watch traffic in real-time, and set up alerts for large data transfers, or unknown IP addresses, so you can see anything suspicious immediately.
Another important step is encryption. Whether data is stored or being sent somewhere, encryption protects sensitive data. But encrypted data is much harder for someone to use, even if they manage to intercept it.
Security tools on devices also help protect your company data. Because employees use different devices to access systems. Data Loss Protection (DLP) tools help prevent important files from being moved outside of the network and tell you if someone tries to do such type of malicious activities. Finally, a well-thought incident response plan of attack for breaches will allow you to react quickly minimize the damage, and make recovery easier.
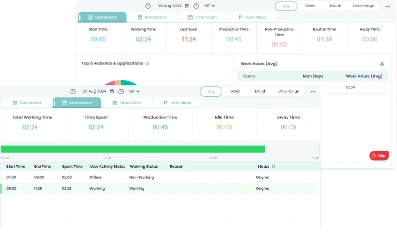
How Time Champ Helps Protect Your Data from Attackers?
The robust data loss protection features in Time Champ protect your data from attackers. You can control website access, configure websites as safe or unsafe, and allow your employees to visit only safe and approved websites. You can control USB access and block unauthorized devices to transfer data.
To track suspicious activities like if any of your employees are accessing the company’s important files without having access permission, Time Champ monitors and tracks your files and alerts you before any hacker steals your important info. You can also limit file upload and download actions to avoid the chance of sensitive data being moved or stolen. Time Champ data loss protection tools are a strong defense against data exfiltration and protect your company’s valuable information from hidden cyber threats.
Protect your organization from data exfiltration risks today!
Try Time Champ now to secure your data and stay one step ahead!
Final Thoughts
Data exfiltration is a risky threat that can compromise your company’s reputation and put your company’s important information at risk. To protect your business from threats, you need to be aware of and use strong security methods in your organization. Encryption, Strong access controls, data loss protection (DLP) tools, and employee awareness are all critical steps to protect sensitive information. By being proactive and taking the appropriate steps, you may make it easier to protect your confidential data from this type of exfiltration threat.
Table of Content
-
 What is Data Exfiltration?
What is Data Exfiltration?
-
 How Does Data Exfiltration Occur?
How Does Data Exfiltration Occur?
-
 Types of Data Exfiltration
Types of Data Exfiltration
-
 The Cost of Data Exfiltration
The Cost of Data Exfiltration
-
 How to Detect Data Exfiltration?
How to Detect Data Exfiltration?
-
 Data Exfiltration Prevention
Data Exfiltration Prevention
-
 How Time Champ Helps Protect Your Data from Attackers?
How Time Champ Helps Protect Your Data from Attackers?
-
 Final Thoughts
Final Thoughts
Related Blogs
Protect your business from data leaks! Learn effective data exfiltration prevention practices to secure sensitive information and stop cyber threats.
Sai Keerthi Uppala | 12 March 2025Protect your business from data theft by understanding key risks and prevention strategies. Learn how to secure sensitive information effectively.
Sai Keerthi Uppala | 12 March 2025A data breach exposes sensitive data to hackers. Learn how breaches happen and the best ways to protect your personal
Jahnavi Pulluri | 12 March 2025Enhance your security with endpoint data loss prevention solutions that guard against data breaches and protect your most valuable assets.
Shabana Shaik | 23 January 2025Stay ahead of cyber threats with our expert guide on endpoint security protection. Explore essential tips and tools to protect
Shabana Shaik | 23 January 2025Explore the real-world examples of Business Email Compromise (BEC) and discover practical prevention tips to protect your business from email
Shabana Shaik | 23 January 2025